How Guardrails Secure and Accelerate K8s Deployments
It’s clear from the latest Cloud Native Computing Foundation survey that containerized environments have become mainstream, increasing automation at scale for companies. But, in the cloud-native environment, changes are constant and runtime is extremely dynamic. And while automation can help eliminate manual work, it can also replicate mistakes and risks at cloud scale. Instead of easing workloads, this can overburden many DevOps teams with both the manual reviews of all the YAML configurations that define what workloads can and cannot do and the rework that comes from fixing that configuration to ensure deployments are free from error, have low risk and comply with internal or external requirements.
That’s why it’s more critical than ever to define and implement automated security guardrails and policies in order to mitigate security and compliance risks. Styra provides organizations with the guardrails necessary to implement a consistent policy framework across the entire app development environment with its Declarative Authorization Service (DAS).
Styra DAS helps customers make the most of their Kubernetes automation
The Styra DAS security and compliance solution for Kubernetes helps companies build, test and distribute Open Policy Agent policy-as-code guardrails at scale, and enables DevOps to eliminate manual overhead, minimize risk and accelerate development.
Styra DAS provides teams with a built-in policy library of best practices and security policies, all sourced from real-world use cases — this limits the need for human intervention and rework, increases pipeline automation and accelerates time to market. In fact, the new Pod Security Policy Pack we’ve introduced today, in addition to the existing Best Practices and PCI DSS 3.2 Policy Packs, speed deployment by eliminating the need to research, identify and implement baseline guardrails/policies for Kubernetes clusters. This new Policy Pack helps DevOps teams configure Kubernetes Pod Security Policies quickly and automatically, ensuring consistent and customized policy enforcement across clusters. The Styra DAS built-in policy library saves time and brainpower, and helps teams get to “day two” faster. 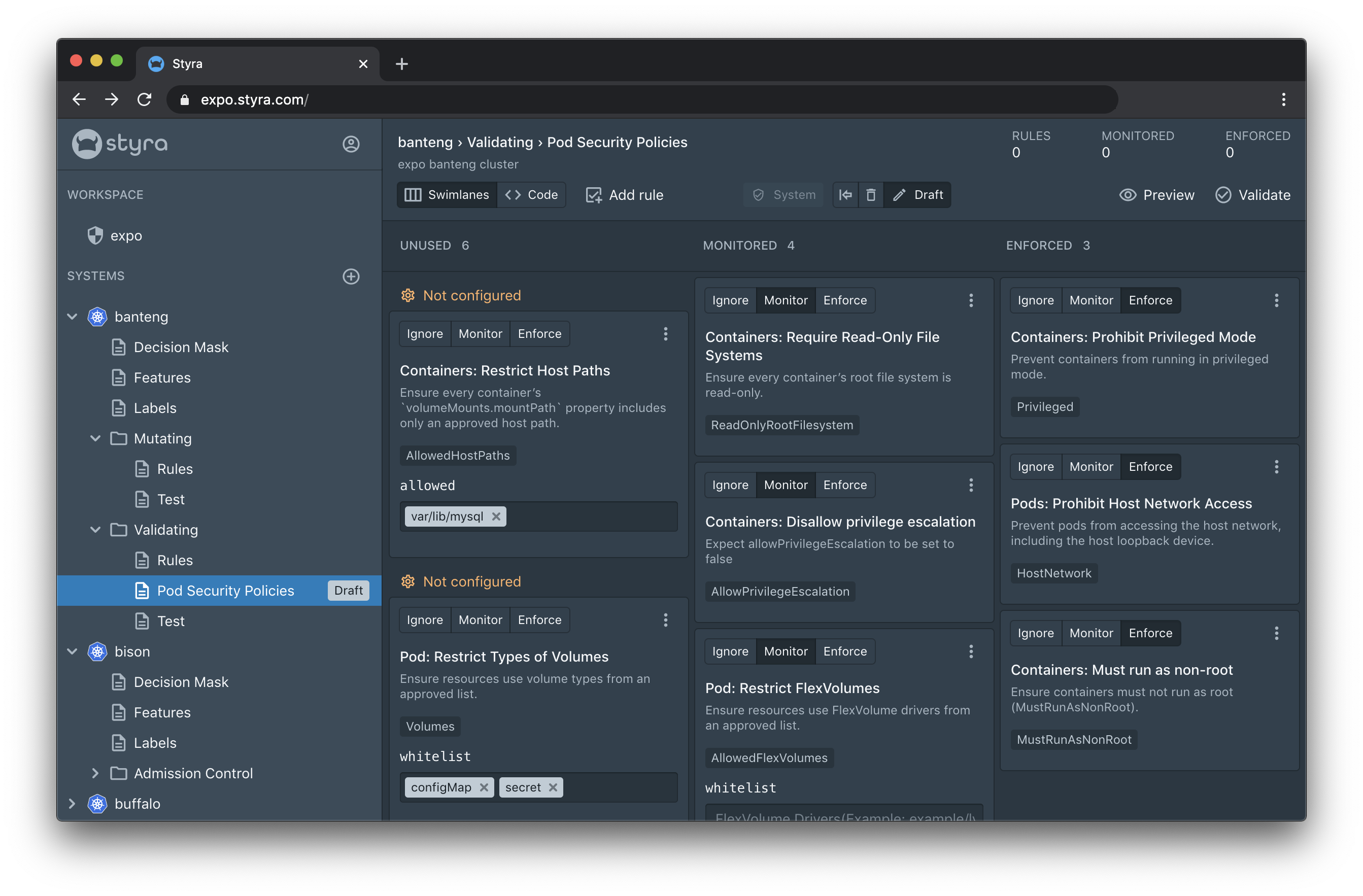
Styra DAS also saves time and brainpower by validating all workloads against custom policy before they get to runtime. And with the new support for Kubernetes mutating webhooks, we’ve enabled policies to go beyond simple “allow or deny,” to automatically append, update or add relevant parameters that ensure workloads are compliant before they reach production. This new feature eliminates manual rework when configuration is incomplete or incorrect, and automates the inclusion of appropriate services/sidecars as necessary, to ensure all runtime networking, proxy and other tools are in place every time. And of course, all policy decisions are monitored and logged to ease security and compliance conversations and audits.
No longer are security and speed at odds with each other. With Styra DAS, DevOps teams make the most of their Kubernetes and CICD pipeline automation so that they can focus on accelerating their differentiated work without wasting cycles or cutting corners on critical but undifferentiated work.
Hard to believe? Let us show you!